my posts
I keep this blog to write down stuff I ran into along the way.WebSEAL LUA http transformation rules with external data warning
This is some additional info on creating LUA transformation rules in WebSEAL, building on this topic: WebSEAL LUA http transformation rules with external data
Read more ...Blue green deployments with WebSEAL stateful junctions
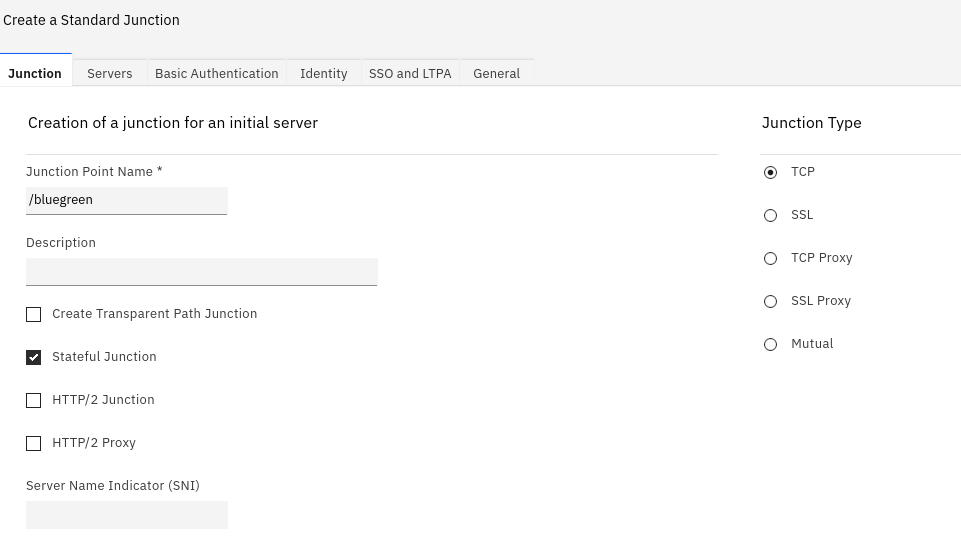
Using stateful junction together with the priority attribute in WebSEAL’s junctions, we can provide a Blue-green deployment mechanism using WebSEAL (or IBM Appliation Gateway (IAG), for that matter)
Read more ...Tip : set negative integer attribute value with pdadmin object modify
I was recently trying to set the value -1 on an object attribute using pdadmin.
A nicer credential viewer for WebSEAL
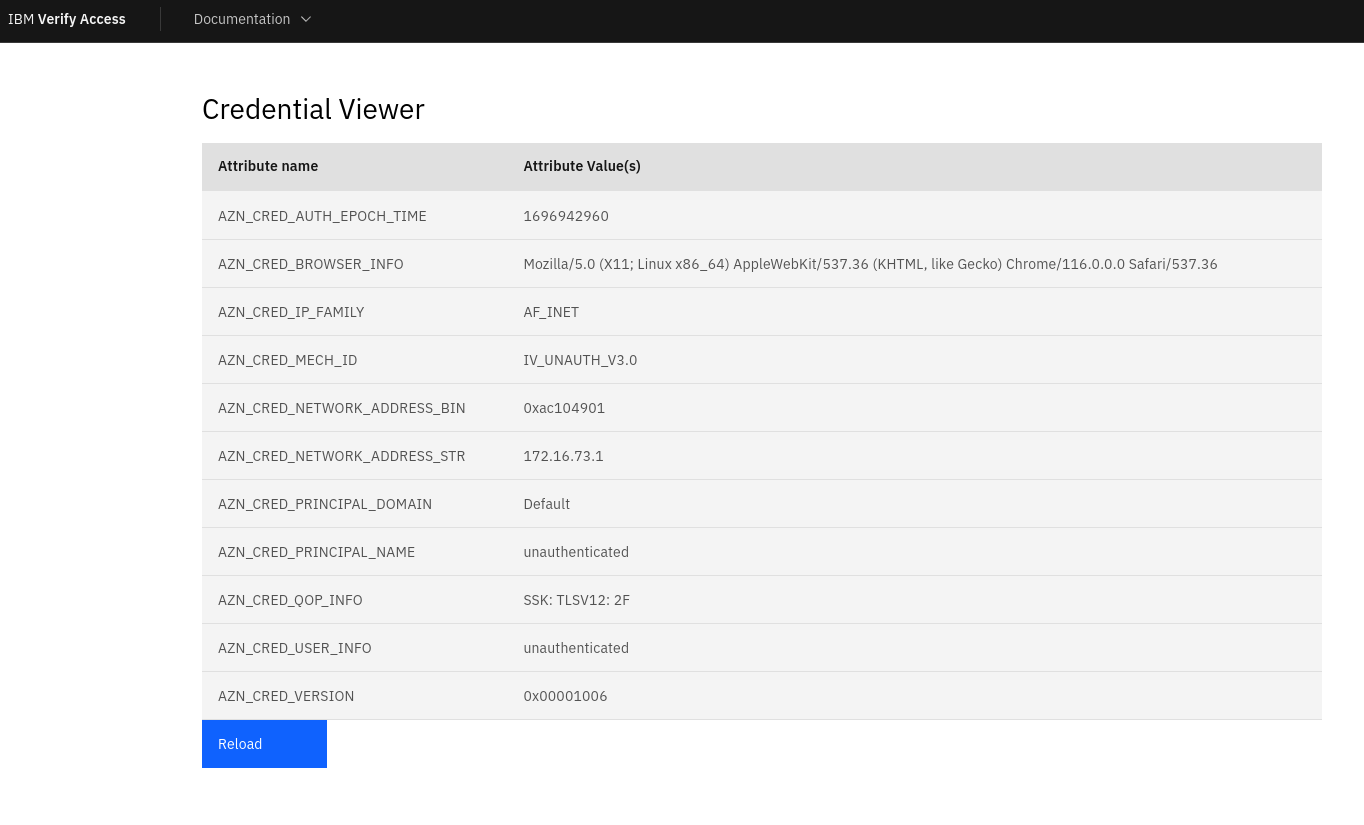
WebSeal also has a credential viewer application, and this comes out of the box with a web interface.
Read more ...WebSEAL AZN Decision viewer
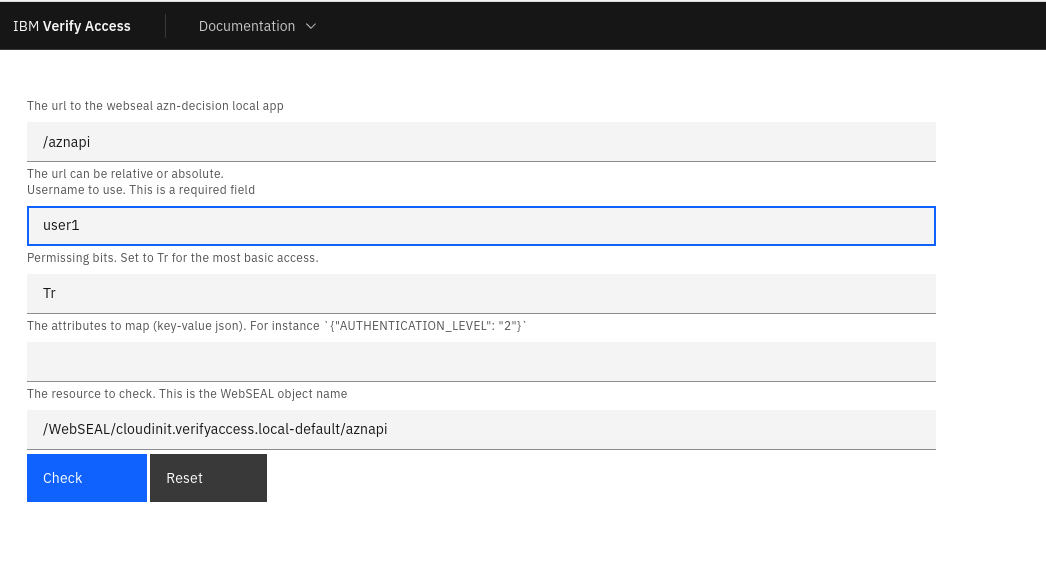
WebSeal comes with a local app these days, that can show you if a particular user (credential) would have access to a WebSEAL resource.
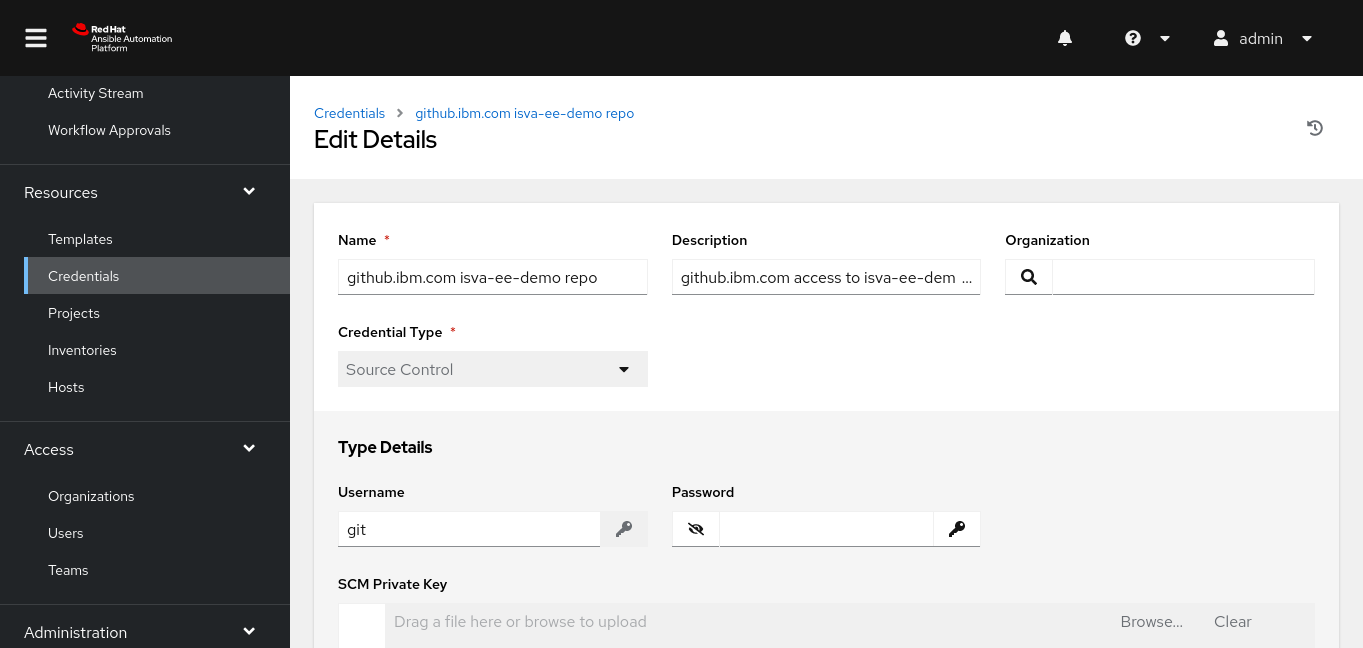
Read more ...Ansible with verify ssl
I ran into a problem trying out the awx.awx collection, to export the assets through Ansible Automation Platform’s api.
Authenticate to WebSphere using the WebSEAL jwt junction
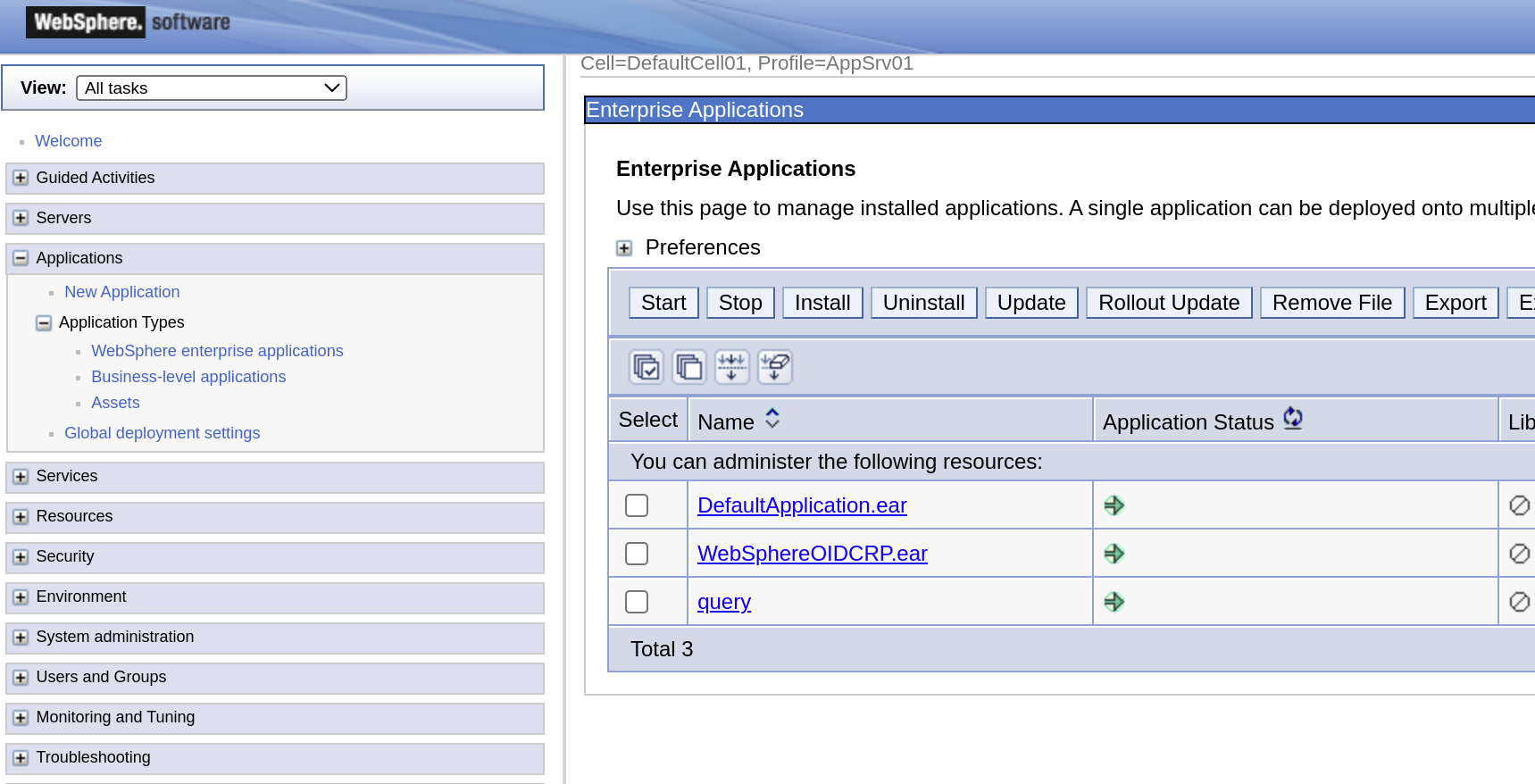
In a recent project, I wanted to quickly setup a jwt junction to a WebSphere Traditional Server (actually to a HCL Portal Server).
Read more ...Ansible Execution Environment for the IBM ISVA Ansible collection revisited
This is a follow-up to an earlier blog entry I wrote.
Read more ...Cloud-init for ISVA 10.0.6 with VMWare workstation
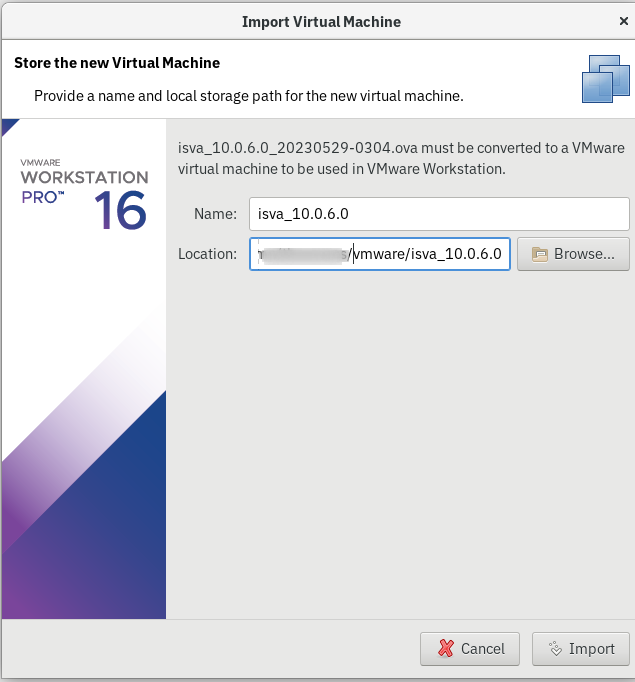
TL;DR The new cloud-init feature in ISVA 10.0.6 cannot be used together with VMWare workstation.
Read more ...Cloud-init in vmware workstation
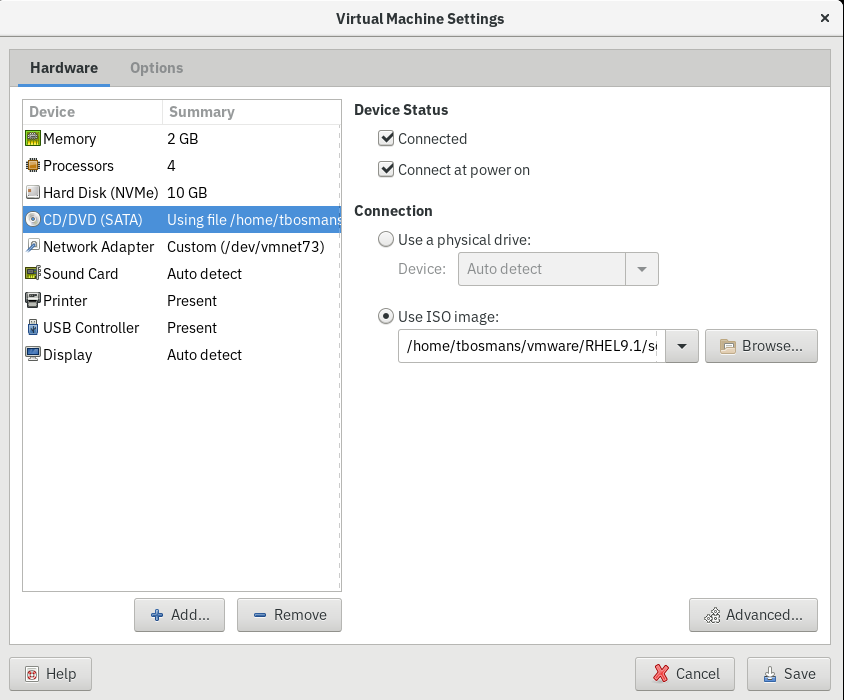
I wanted to quickly setup a virtual machine on my laptop using VMWare Workstation and Redhat 9. I generally don’t think about that too much and do that manually (shame on me).
Read more ...WebSEAL LUA http transformation rule for logging
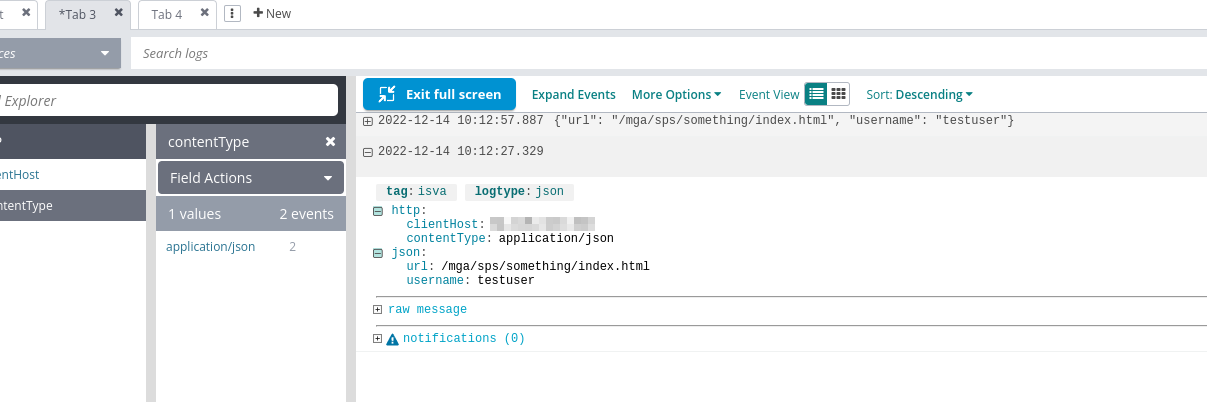
This is a small follow-up post to my previous post on LUA transformation rules to retrieve external data WebSEAL LUA http transformation rules with external data
Read more ...